Security Operations
Manage identity security, automated remediation, incident response playbooks, and Azure resource scanning from a unified security operations console.
Identity Security
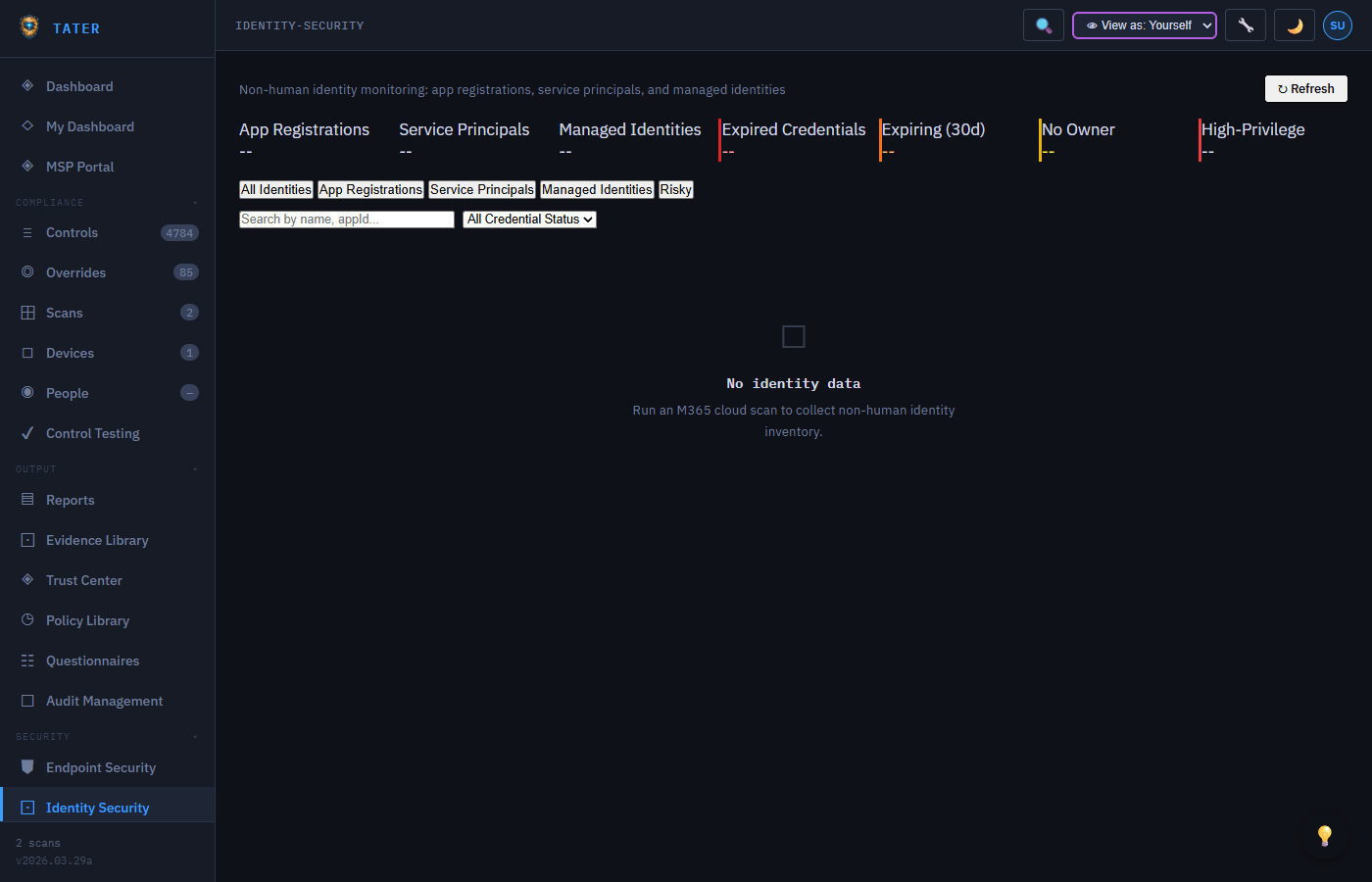
The Identity Security module provides visibility into identity-related risks across your Microsoft 365 environment:
Dashboard Overview
- Risky Users: Users flagged by Entra ID Identity Protection with risk levels (High, Medium, Low)
- MFA Status: Breakdown of MFA enrollment across your user base
- Privileged Accounts: Count of users with privileged roles (Global Admin, Security Admin, etc.)
- Stale Accounts: Users who have not signed in within a configurable period
- Guest Users: External guest accounts with access to your tenant
Identity Controls
Identity-related compliance controls from CIS and CISA SCuBA are grouped together for focused monitoring:
- Conditional Access policy evaluation
- Password policy compliance
- Admin account separation and protection
- Self-service password reset (SSPR) configuration
- Legacy authentication blocking
- Privileged role assignment tracking
Recommendations
Based on your identity posture, TATER generates prioritized recommendations:
- Enable MFA for remaining users
- Review and reduce privileged role assignments
- Disable or remove stale guest accounts
- Implement conditional access policies for risky sign-ins
- Block legacy authentication protocols
Automated Remediation
TATER includes one-click automated remediation for failing compliance controls. The remediation system uses a two-runbook architecture in Azure Automation to handle both Graph API and Exchange Online operations.
How It Works
- Identify: Navigate to a failing control on the Controls page and click the Remediate button
- Confirm: Review the remediation description and any required parameters in the confirmation modal
- Execute: TATER triggers the remediation webhook, which starts the Azure Automation runbook
- Monitor: The modal shows real-time status polling (5-second intervals, 10-minute timeout)
- Verify: Once complete, run a new scan to verify the control now passes
Architecture
The remediation system uses two Azure Automation runbooks:
| Runbook | Runtime | Purpose |
|---|---|---|
| Run-Remediation | PS 7.2 | Primary runbook. Handles Graph API remediations and auto-delegates EXO-dependent scripts |
| Run-Remediation-EXO | PS 5.1 | Companion runbook for Exchange Online, Defender, and Security & Compliance remediations |
The primary runbook scans each remediation script for Exchange cmdlet patterns. If EXO cmdlets are detected, it automatically delegates execution to the PS 5.1 companion runbook.
Remediation Catalog
TATER includes 52 pre-built remediation scripts covering:
| Category | Scripts | Examples |
|---|---|---|
| Defender | 11 | Safe Links, Safe Attachments, DKIM, SPF, spam filters |
| Exchange Online | 6 | Auditing, modern auth, MailTips, SMTP AUTH |
| SharePoint | 5 | External sharing, guest reshare, infected files |
| Entra ID | 9 | Idle timeout, app registration, SSPR, guest invite |
| Power BI | 2 | Publish to web, resource key auth |
| Purview | 1 | Retention policies |
| SCUBA | 17 | Preset security, DMARC, alerts, sharing, audit |
| Teams | 2 | Guidance-only (requires delegated auth) |
Teams remediation scripts provide guidance only. The underlying Cs* cmdlets require delegated authentication, which cannot be automated in Azure Automation runbooks.
Enabling Remediation
Automated remediation must be enabled per organization:
- Navigate to Settings > Integrations
- Enable the Automated Remediation toggle
- Enter the Azure Automation webhook URL for the Run-Remediation runbook
- Enter the App Registration Client ID used by the runbook
- Test the connection with the Test button
For detailed setup instructions including Azure Automation configuration, managed identity permissions, and blob storage, see the Azure Runbooks guide and the Remediation Setup Guide in the Docs folder.
Incident Response Playbooks
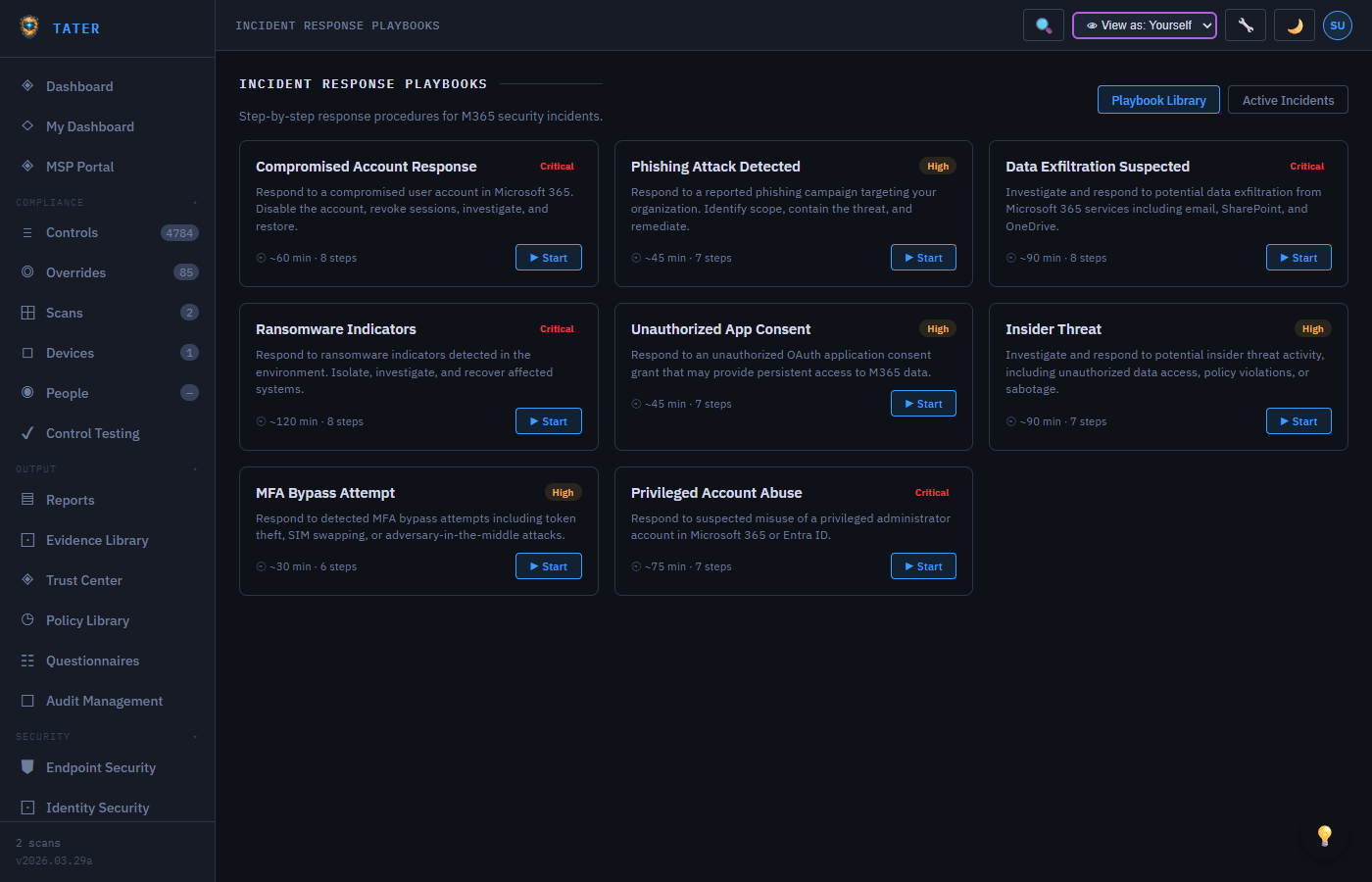
Create and manage incident response playbooks with step-by-step response procedures for common security incidents.
Playbook Library
- Pre-built Playbooks: Common incident types (phishing, malware, data breach, account compromise, DDoS)
- Custom Playbooks: Create organization-specific response procedures
- Version Control: Track playbook revisions and approvals
- Owner Assignment: Assign playbook owners responsible for keeping procedures current
Playbook Structure
Each playbook contains structured response phases:
- Detection & Analysis: How to identify and confirm the incident
- Containment: Immediate actions to limit the impact
- Eradication: Steps to remove the threat
- Recovery: Restoring normal operations
- Post-Incident: Lessons learned and process improvements
Activating a Playbook
When an incident occurs, activate a playbook to track the response:
- Select the relevant playbook and click Activate
- Assign responders to each phase and step
- Track completion of each step with timestamps
- Document findings and decisions at each phase
- Generate a post-incident report from the completed playbook
Azure Resource Scanning
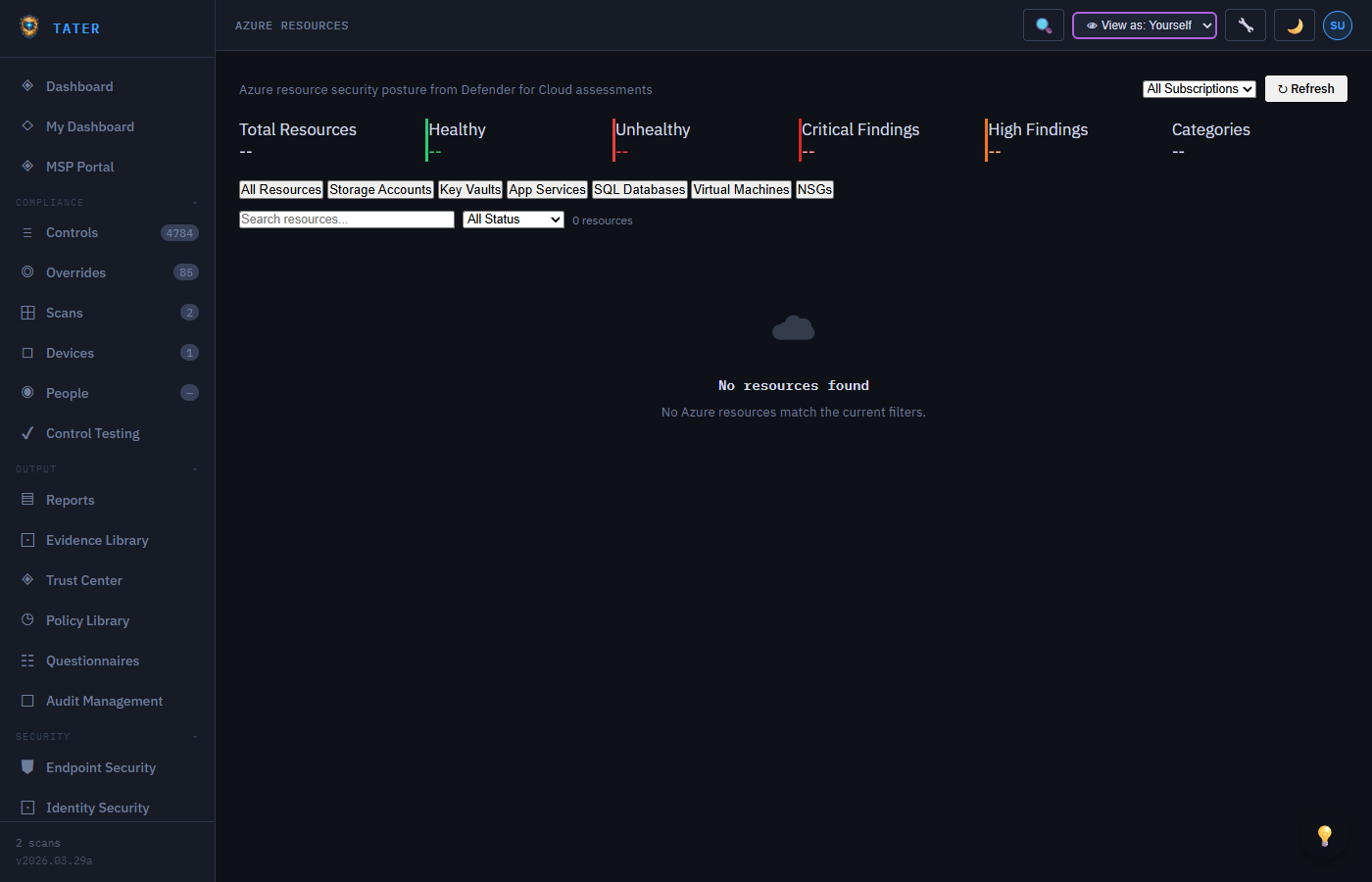
Scan and monitor Azure resource configurations for compliance with security best practices.
What Gets Scanned
- Resource Groups: Organization and tagging compliance
- Storage Accounts: Encryption, access controls, network rules, secure transfer
- Key Vaults: Access policies, soft delete, purge protection
- Virtual Machines: Disk encryption, network security groups, update status
- App Services: HTTPS enforcement, TLS version, authentication settings
- SQL Databases: TDE, auditing, threat detection, firewall rules
- Network Security Groups: Inbound/outbound rule analysis
Understanding Results
Azure resource scan results integrate with the standard compliance view:
- Each resource check maps to a compliance control
- Results are displayed alongside M365 compliance data on the dashboard
- Failing resources are linked to specific remediation guidance
- Cross-framework mapping shows how Azure controls satisfy NIST, ISO, and SOC 2 requirements
Setup
To enable Azure resource scanning:
- Configure an app registration with Reader role on target subscriptions
- Store the credentials in TATER Settings > Tenants
- Enable the Azure Resources feature in Settings > Features
- Trigger a scan from the Azure Resources page or schedule it alongside M365 scans
Identity Threat Detection & Response (ITDR)
The ITDR module surfaces identity-layer threats from Microsoft Entra ID and Microsoft Defender — enabling your team to investigate and respond to suspicious sign-ins, risky users, and anomalous identity behaviors directly within TATER.
ITDR Alerts
- Alert ingestion: Pull risky user events, sign-in anomalies, and identity protection alerts from Entra ID Risk Detections via the Graph API scan
- Severity classification: Alerts classified as Critical, High, Medium, or Low based on the Entra ID risk level and detection type
- Status workflow: New → Investigating → Resolved / False Positive with investigation notes and assignee tracking
- Source user tagging: Each alert links to the affected user's UPN and Entra ID object ID for quick lookup
ITDR Playbooks
Attach standardized response procedures to ITDR alert categories. When an alert is created, the matching playbook appears inline with step-by-step investigation and containment guidance. Playbooks can be created in the Incident Response Playbooks page and linked to ITDR alert types.
Investigation Workflow
- Alert created (automatically via scan or manually by analyst)
- Analyst assigns the alert and sets status to Investigating
- Investigation notes field captures timeline, findings, and remediation actions taken
- Related sign-ins list shows associated sign-in events (IP, location, device)
- Alert resolved or marked as False Positive with closing notes
- All state changes written to the Activity Log for audit trail
Multi-Cloud Security Posture
Beyond Microsoft 365 and Azure, TATER's Multi-Cloud module extends compliance visibility to AWS and GCP environments — providing a unified security posture dashboard across your entire cloud estate.
Cloud Account Management
- Register AWS accounts (Access Key + Secret, or cross-account IAM role ARN) and GCP projects (Service Account JSON)
- Credentials are encrypted at rest using AES-256-GCM
- Multiple accounts per cloud provider are supported for multi-account organizations
- Account health status (Connected, Error, Not Configured) shown on the posture dashboard
Cloud Posture Scans
Trigger on-demand posture scans against registered cloud accounts. Scan results are evaluated against cloud security benchmarks:
- AWS: CIS Amazon Web Services Foundations Benchmark, AWS Security Hub standards
- GCP: CIS Google Cloud Platform Foundation Benchmark
- Results are displayed per-account with pass/fail/unknown counts and severity breakdown
- Findings map to TATER's unified control catalog where framework mappings exist
Understanding Results
- Pass rate shown per cloud account and per framework section
- Critical findings highlighted with recommended remediation steps
- Cross-cloud posture summary on the Security Posture overview page
- Results included in Executive Report when the Multi-Cloud module is enabled
Data Classification & Privacy
See also: GRC Modules → Data Classification & Privacy for full documentation.
The Data Classification module provides a structured inventory of your organization's data assets, supporting GDPR, HIPAA, and ISO 27001 data governance requirements:
- Data Asset Inventory: Catalog data stores (databases, file shares, SaaS applications) with classification labels: Public, Internal, Confidential, or Restricted
- Data Flow Mapping: Document how data moves between systems, including cross-border transfers and third-party sharing
- Privacy Impact Assessments (PIA): Structured PIA workflow with risk assessment, stakeholder review, and approval tracking
- Retention Policies: Define retention periods and disposition actions per data category, with automated reminder tracking
- Classification Labels: Public, Internal, Confidential, Restricted — each with configurable handling requirements and access controls
 TATER
TATER