GRC Modules Guide
Complete guide to all Governance, Risk, and Compliance modules in TATER: Risk Register, Exception Management, Audit Management, BCP/DR, Data Classification, Training, Control Testing, Vendor Management, Questionnaires, Change Requests, Regulatory Changes, and Access Reviews.
Risk Register & Heat Map
The Risk Register provides a centralized catalog of organizational risks with quantitative scoring, treatment tracking, and a visual 5x5 heat map.
Key Features
- 5x5 Heat Map: Interactive likelihood vs. impact grid showing risk distribution across severity zones
- Quantitative Scoring: ALE = SLE x ARO (Annual Loss Expectancy = Single Loss Expectancy x Annual Rate of Occurrence)
- Treatment Plans: Four treatment options: Mitigate, Accept, Transfer, Avoid
- Residual Risk: Track residual risk after treatment measures are applied
- Control Linkage: Bidirectional linkage between risks and compliance controls
- Categories: Organize risks by category (Operational, Strategic, Compliance, Financial, Technical, Reputational)
Creating a Risk Entry
Click New Risk
Navigate to the Risk Register and click New Risk to open the creation form.
Define the risk
Enter the risk title, description, category, and risk owner. Provide detailed context about the threat and its potential impact.
Score likelihood and impact
Rate both likelihood (1-5) and impact (1-5). The heat map cell updates in real-time. Optionally enter SLE and ARO for quantitative ALE calculation.
Select treatment
Choose a treatment option (Mitigate, Accept, Transfer, Avoid) and document the treatment plan. Link related compliance controls for traceability.
Set residual risk
After treatment is applied, reassess and record residual likelihood and impact scores.
Click any cell in the heat map to filter the risk list to only show risks at that likelihood/impact intersection. Click again to clear the filter.
Exception & Waiver Management
Manage formal exception requests for compliance requirements that cannot be met due to business constraints, with structured approval workflows and automatic expiry enforcement.
Exception Workflow
- Request: Submit an exception request with the affected control, business justification, and proposed compensating controls
- Review: The request enters a multi-level approval chain (OrgAdmin, CISO, Risk Committee)
- Approve/Deny: Each approver reviews and provides their decision with comments
- Monitor: Approved exceptions are tracked with expiry dates and renewal reminders
- Renew or Close: Before expiry, the exception owner can renew with updated justification or close the exception
Exception Request Fields
| Field | Description |
|---|---|
| Control | The compliance control requiring an exception |
| Justification | Business reason why the requirement cannot be met |
| Compensating Controls | Alternative measures implemented to reduce risk |
| Expiry Date | When the exception expires and must be renewed or resolved |
| Risk Level | Residual risk with the exception in place |
| Owner | Person responsible for monitoring the exception |
Exceptions approaching their expiry date trigger renewal reminders 30 days, 14 days, and 7 days before the deadline. Expired exceptions are automatically flagged and removed from active override calculations.
Audit Management
Plan and manage internal and external audit engagements with finding tracking, evidence collection, and calendar management.
Planning an Audit
- Navigate to Audits and click New Audit
- Define the audit: name, type (Internal/External), scope, and objectives
- Set target dates: planned start, planned end, and report deadline
- Assign auditors from your team or external contacts
- Select the frameworks and controls in scope for the audit
Managing Findings
During the audit, record findings as they are identified:
- Severity: Critical, Major, Minor, Observation
- Affected Controls: Link findings to specific controls
- Remediation Plan: Document the corrective action plan with target dates
- Status Tracking: Open, In Progress, Remediated, Verified, Closed
- Evidence: Attach supporting evidence to findings
Evidence Collection
Request evidence from control owners during the audit process:
- Click Request Evidence on an audit finding or control
- Select the evidence type needed (screenshot, document, configuration export, etc.)
- Assign the request to the control owner with a due date
- The owner receives a notification and can upload evidence directly
- Track request status: Requested, In Progress, Submitted, Reviewed
Audit Calendar
The audit calendar view shows all past and upcoming audit engagements in a timeline format. Use it to plan audit cadence and avoid scheduling conflicts.
Business Continuity & Disaster Recovery
Manage BCP/DR plans with business impact analysis, RTO/RPO tracking, and test exercise management.
Plan Management
- Plan Library: Maintain multiple BCP/DR plans with version control
- Approval Workflows: Plans go through review and approval before activation
- Version History: Track changes across plan revisions
- Distribution: Share approved plans with designated team members
Business Impact Analysis (BIA)
Document critical business processes and their recovery requirements:
| BIA Field | Description |
|---|---|
| Process Name | The business process being analyzed |
| Criticality | Mission Critical, Business Critical, Important, Normal |
| RTO | Recovery Time Objective -- maximum acceptable downtime |
| RPO | Recovery Point Objective -- maximum acceptable data loss |
| Dependencies | Systems, applications, and personnel required |
| Impact Assessment | Financial, operational, and reputational impact at various time intervals |
Test & Exercise Tracking
Track BCP/DR test exercises and their outcomes:
- Exercise Types: Tabletop, Walkthrough, Simulation, Full Test
- Results: Actual RTO/RPO achieved vs. targets
- Lessons Learned: Document findings and improvement actions
- Frequency: Track when the last test was performed and when the next is due
RTO/RPO Monitoring
The BCP/DR dashboard compares actual recovery performance against defined targets:
- Green: Actual recovery met or exceeded the objective
- Yellow: Actual recovery was within 120% of the objective
- Red: Actual recovery exceeded the objective by more than 20%
Data Classification & Privacy
Maintain a data asset inventory with classification labels, flow mapping, privacy impact assessments, and retention policy management.
Data Asset Inventory
Catalog all data assets in your organization:
- Asset Name: Name of the data asset or system
- Classification: Public, Internal, Confidential, Restricted
- Data Type: PII, PHI, Financial, Intellectual Property, etc.
- Owner: Data owner responsible for classification decisions
- Storage Location: Where the data resides (cloud, on-premises, hybrid)
- Encryption Status: At rest and in transit encryption status
Data Flow Mapping
Map how data flows between systems in your organization:
- Define source and destination systems
- Document the data types that flow between systems
- Identify cross-border data transfers for regulatory compliance
- Highlight flows that involve sensitive data classifications
Privacy Impact Assessments (PIA)
Conduct privacy impact assessments for new systems or processes:
- Create a new PIA and describe the system or process being assessed
- Identify the personal data collected and processed
- Assess the privacy risks and their likelihood and impact
- Document mitigating measures and residual risk
- Submit for review and approval by the Data Protection Officer
Retention Policy Management
Define and track data retention policies:
- Set retention periods by data classification level
- Track disposition schedules and upcoming deletions
- Document legal hold requirements that override standard retention
- Generate disposition reports for audit compliance
Security Awareness Training
Manage security awareness training campaigns with completion tracking, phishing simulation results, and audit-ready compliance reports.
Campaign Management
- Navigate to Training and click New Campaign
- Define the campaign: name, required courses, target audience, deadline, and completion threshold
- Assign target groups (all employees, specific departments, new hires)
- Set the campaign as mandatory or optional
- Activate the campaign to begin tracking
Completion Tracking
Track per-employee completion status with dashboard KPI cards:
- Completion Rate: Percentage of target audience who completed all required courses
- Overdue: Count of employees past the deadline who have not completed training
- In Progress: Employees who have started but not finished
- Not Started: Employees who have not begun training
Phishing Simulation Results
Import phishing simulation results from third-party tools and track trends:
- Click rate, report rate, and data submission rate per campaign
- Trend analysis across multiple simulation campaigns
- Department-level breakdown showing which teams need additional training
- Repeat offender identification for targeted intervention
Audit Evidence
Training completion records serve as audit evidence for compliance frameworks that require security awareness training (NIST 800-53 AT-2, ISO 27001 A.7.2.2, SOC 2 CC1.4).
Control Testing Automation
Schedule and execute control tests with reusable procedures, historical results tracking, and automatic gap detection.
Test Scheduling
Configure automated test schedules for each control:
- Frequency: Daily, Weekly, Monthly, Quarterly, Annually
- Scope: Individual controls or groups of controls
- Assignments: Assign test execution to specific team members
- Notifications: Alerts when tests are due or overdue
Test Procedure Library
Build a reusable library of test procedures:
- Document step-by-step test procedures for each control
- Define pass/fail criteria with clear thresholds
- Include expected evidence and documentation requirements
- Reuse procedures across multiple test cycles
Historical Results & Trends
- View test results over time with trend charts showing effectiveness
- Identify controls that consistently fail tests for remediation prioritization
- Generate test reports for audit evidence
- Track tester notes and observations alongside pass/fail status
Automatic Gap Detection
Failed control tests automatically feed into the remediation workflow:
- Failed tests generate gap notifications to control owners
- Gaps are linked to the failing control for remediation tracking
- SLA timers start based on the control's severity level
Vendor Risk Management
Manage third-party vendor relationships with risk tiering, assessment tracking, and continuous monitoring.
Vendor Inventory
- Vendor Name: Company name and primary contact
- Risk Tier: Critical, High, Medium, Low based on data access and business dependency
- Services: Services provided by the vendor
- Data Access: What types of data the vendor can access
- Contract Status: Active, Under Review, Terminated
- Last Assessment: Date of most recent risk assessment
Risk Assessments
- Select a vendor and click New Assessment
- Complete the assessment questionnaire (security controls, certifications, incident history)
- Review vendor-provided evidence (SOC 2 reports, penetration test results, etc.)
- Score the vendor across security domains
- Generate an assessment report with recommendations
Continuous Monitoring
- Track vendor certification expiry dates
- Monitor vendor security ratings from external sources
- Set reassessment reminders based on risk tier frequency
- Document vendor incidents and their resolution
Access Reviews
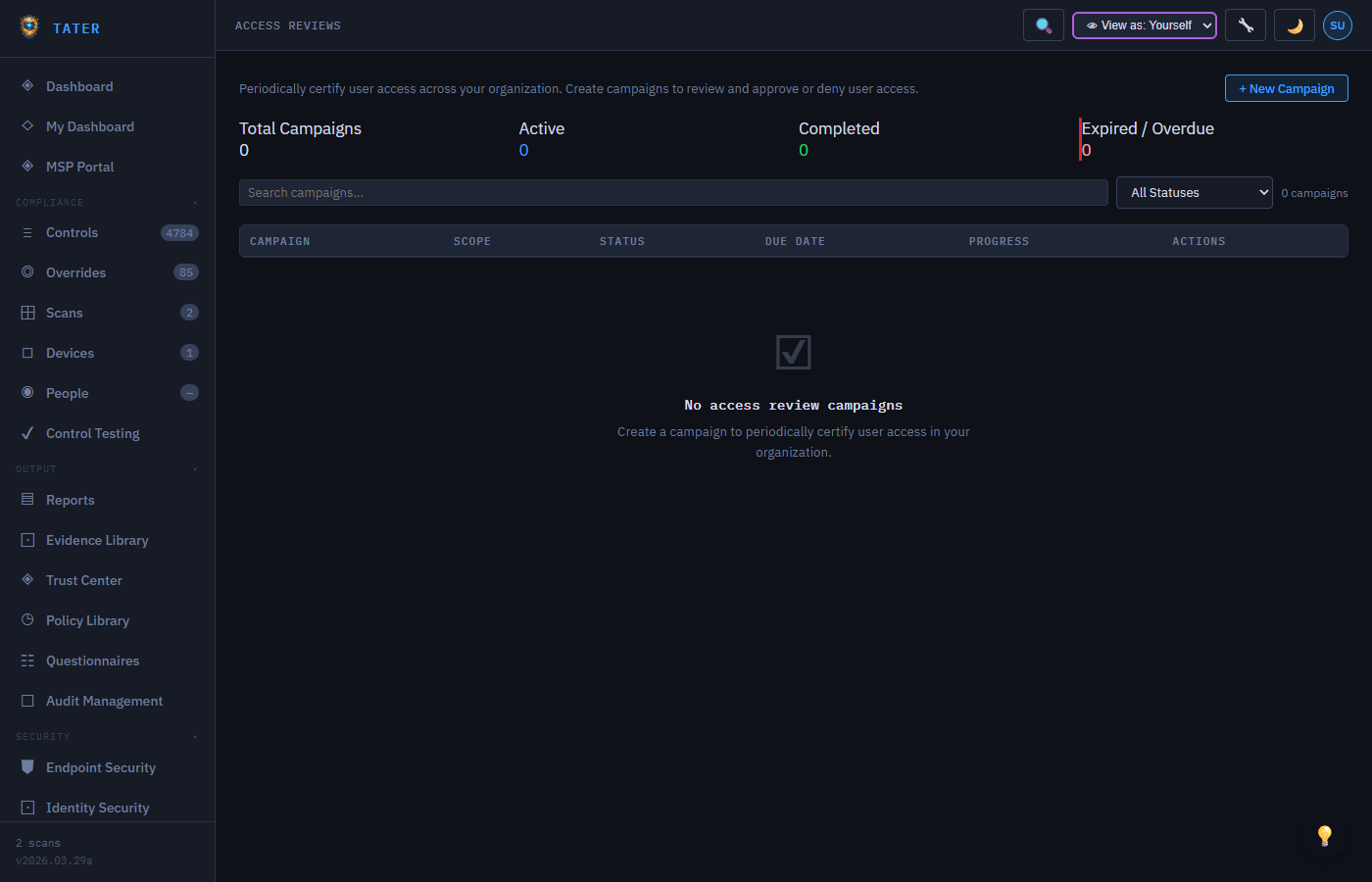
Conduct periodic access reviews to ensure users have appropriate access levels across your organization's systems.
Review Campaigns
- Navigate to Access Reviews and click New Review
- Define the scope: which systems, roles, or user groups to review
- Assign reviewers (typically managers or system owners)
- Set the review deadline
- Activate the campaign to begin the review process
Review Process
- Reviewers receive notifications with a list of users to review
- For each user, the reviewer can: Approve (keep access), Revoke (remove access), or Flag (escalate for further review)
- Reviewers can add comments explaining their decisions
- Bulk actions allow approving or revoking multiple users at once
Review Reports
- Completion rate tracking per reviewer
- Summary of approved, revoked, and flagged access
- Audit trail of all review decisions with timestamps
- Overdue reviews highlighted for escalation
Change Control
The Change Control module enforces a structured approval workflow before high-impact configuration changes are applied to your environment — providing a documented audit trail for every modification.
How It Works
- Automatic routing by impact: Low and Medium impact changes are auto-approved and logged immediately. High and Critical impact changes enter a Pending state and require OrgAdmin approval.
- Scan-detected changes: When a new scan result differs from the previous scan for a control, TATER automatically creates a change request of type
scan-detected— giving you an audit record without manual entry. - Manual change requests: Users can log planned changes (type
manual) before making changes, providing a pre-authorization paper trail. - MCP integration: The
list_pending_changesandcreate_change_requestMCP tools allow AI agents to query pending changes and log new ones as part of automated workflows.
Approving and Rejecting Changes
- OrgAdmin+ users see an Approve and Reject button on each pending change request
- Approval requires an optional Approval Note explaining the decision
- Approved changes record the approver's name, OID, and timestamp
- Rejected changes are closed with the rejection reason visible in the audit log
Change Request Fields
| Field | Description |
|---|---|
| Control ID | The TATER control this change is associated with (e.g., ENT_001) |
| Description | What is changing and why (minimum 10 characters) |
| Impact | Low, Medium, High, or Critical — determines auto-approval vs. manual review |
| Type | manual (user-initiated) or scan-detected (automatic from scan comparison) |
| Status | Pending, Approved, Rejected, or Auto-Approved |
CSV Export
All change requests can be exported to CSV for SOC 2, ISO 27001, or internal audit evidence. The export includes all fields, approval timestamps, and approver details.
Custom Control Frameworks
TATER's framework builder lets you define completely custom compliance frameworks alongside the built-in CIS, NIST, ISO, and SCUBA frameworks — enabling organizations to encode internal policy requirements, customer commitments, or proprietary standards into the same compliance engine.
Framework Builder
- Navigate to Governance & Risk → Custom Frameworks to open the builder
- Define domains (e.g., Identity, Data Protection, Network) as top-level groupings
- Add custom control definitions within each domain with threshold logic in the V2 threshold engine
- Map custom controls to standard frameworks (CIS, NIST 800-53, ISO 27001) for cross-framework gap analysis
Import / Export
- Export a custom framework as JSON for backup or distribution to other organizations
- Import a JSON framework package — useful for MSPs distributing a standard client framework across managed accounts
- Imported frameworks appear in the same framework list as built-in frameworks
Custom Control Definitions
Each custom control supports the same threshold types as the V2 engine:
- Boolean: Pass/fail based on a true/false value
- Compare: Numeric comparison (greater than, less than, equal to)
- Includes / Excludes: Check whether a value appears in a list
- Count: Evaluate the count of items against a threshold
- Regex: Pattern matching against string values
- Composite: Combine multiple thresholds with AND/OR logic
Regulatory Change Management
See the dedicated Regulatory Change Management guide for full documentation on tracking framework updates, assessing impact on your controls, and managing the transition to new requirements.
In brief, this module lets you:
- Curate a feed of regulatory and framework updates (CIS benchmark revisions, NIST updates, new CISA SCuBA baselines)
- Tag each change as New Requirement, Updated Requirement, Retired Requirement, or Clarification
- Set Effective Dates and track compliance deadlines on the GRC Calendar
- Link affected controls to the change record for gap analysis
Auditor Portal
The Auditor Portal provides time-limited, read-only access to compliance evidence packages for external auditors — without requiring auditors to have a TATER account.
Access Tokens
- Generate access tokens from Administration → Audit Management → Auditor Portal
- Each token is scoped to a specific framework (e.g., SOC 2, ISO 27001) and expires after a configurable period (1–90 days)
- Tokens can be revoked at any time before expiry
- Access events are logged (timestamp, IP address) for your audit trail
What Auditors See
- Framework compliance summary and control-by-control status for the scoped framework
- Evidence comments attached to each control (added via the AI Analyst or manually)
- Risk acceptances and overrides with justification text
- Policy documents in the Policy Library (with Published status)
- Your organization branding (logo, company name)
Audit Snapshots
Point-in-time snapshots capture compliance state at a specific moment — useful for year-end audits or regulatory submission deadlines. Snapshots are immutable records that preserve the compliance posture at the time of generation even as future scans change the live state.
 TATER
TATER