Running Scans
TATER supports M365 cloud audits, Windows OS compliance scanning, and endpoint vulnerability scanning. This guide covers all scan types, execution methods, grouping, deduplication, and export.
Scan Overview
TATER evaluates compliance across three primary scan types:
| Scan Type | What It Covers | How It Runs |
|---|---|---|
| M365 Cloud | Exchange Online, SharePoint, Teams, Defender, Entra ID, Purview, Power BI, Power Platform | Azure Automation runbook or server-side trigger |
| Endpoint | MDE vulnerabilities, Intune compliance, CISA KEV, software inventory | Azure Automation runbook (daily schedule) |
| OS/Agent | Windows CIS benchmarks, macOS security controls, Linux security controls (20 controls each), registry, services, firewall, audit policy | TATER Agent on each endpoint |
Importing Scans
Scan results can be imported into TATER through several methods:
File Upload
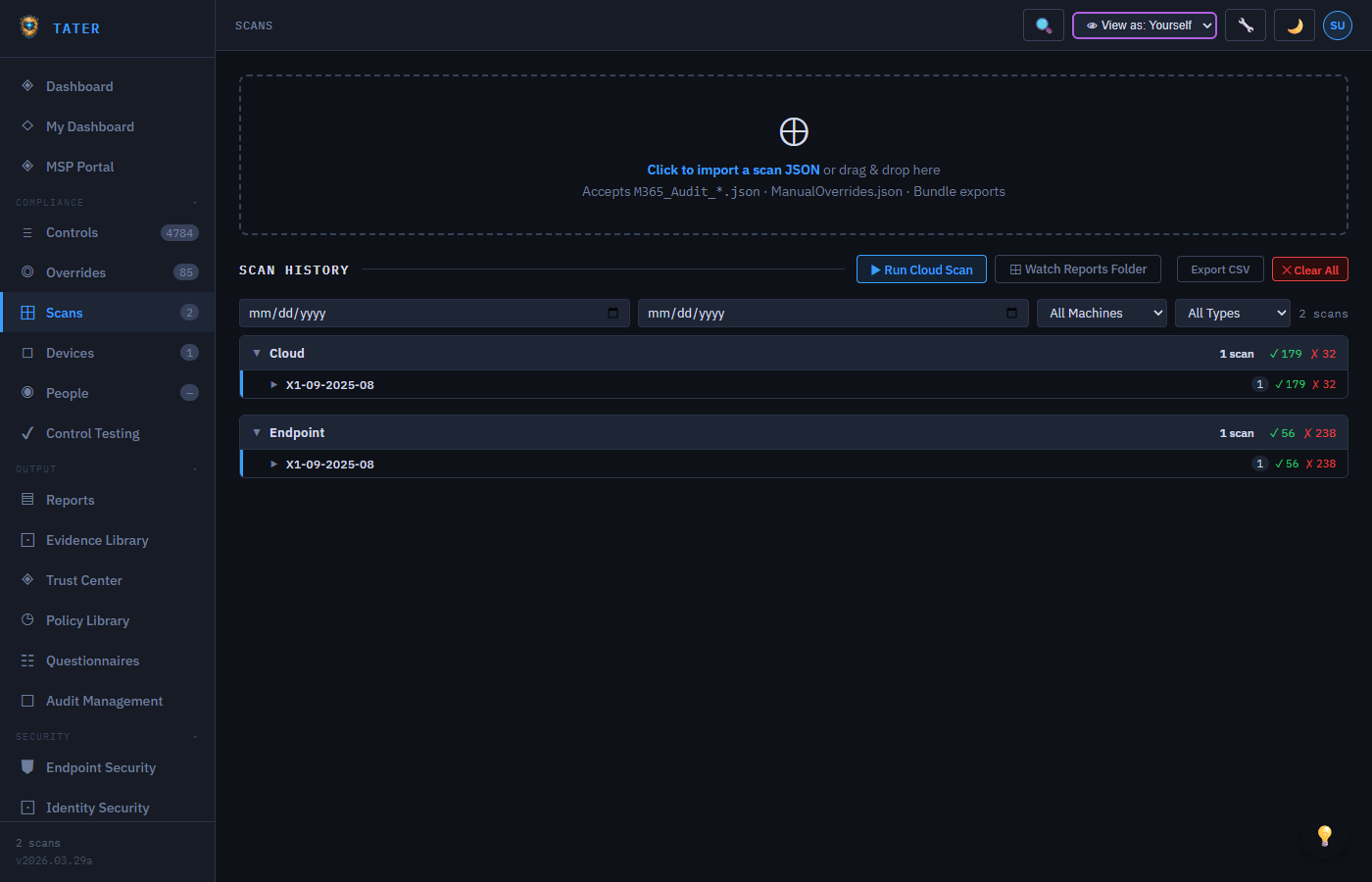
Navigate to Scans
Go to the Scans page from the sidebar navigation.
Click Import Scan
Click the Import Scan button at the top of the page.
Select the JSON file
Browse to and select the scan results JSON file produced by the audit script or Azure Automation runbook.
Review and confirm
TATER validates the file format, checks for duplicates, and displays a summary before importing.
Automatic Upload (Runbooks)
When using Azure Automation runbooks, scan results are automatically uploaded to the TATER API using the POST /scans/upload endpoint. The runbook authenticates using an API key configured in Azure Automation variables.
# Runbook auto-uploads results to TATER API
# No manual import needed when using Azure Automation
# Configure these Automation Variables:
# ApiBaseUrl = "https://api.tatersecurity.com"
# ApiKey = "your-api-key"
# OrganizationId = "your-org-id"Server-Side Cloud Scan Trigger
If you have stored tenant credentials in TATER, you can trigger a cloud scan directly from the browser without needing Azure Automation:
- Navigate to Scans and click Run Scan
- Select the tenant credentials to use (configured in Settings > Tenants)
- Choose the scan scope (full or specific applications)
- Click Start Scan to begin the server-side scan
- Monitor progress in the scan status panel; results appear automatically when complete
Server-side scans use the POST /scans/run API endpoint and require stored tenant credentials with appropriate Graph API permissions. See Settings > Tenants for credential configuration.
Scan Grouping
The Scans page always groups scans by type, with the following group order:
- Cloud Runbook -- Scans from Azure Automation runbooks
- Cloud -- Server-side or manual cloud scans
- Endpoint -- MDE/Intune vulnerability scans
- Speed Test -- Network speed test results from agents
Within each group, scans are sorted by the user-selected sort column (date, pass rate, etc.). The primary sort is always by type group, with user-selected sorting applied as a secondary sort within each group.
Each scan row displays the date (including time), scan type, machine name, framework, pass count, fail count, and compliance percentage.
Scan Comparison
Compare two scans side-by-side to identify what changed between scan cycles:
- Select two scans using the checkboxes on the scan list
- Click Compare in the toolbar
- The comparison view shows controls that changed status (Pass to Fail, Fail to Pass, new controls, removed controls)
- Use this to investigate compliance drift and understand the impact of configuration changes
Scan Deduplication
TATER automatically detects and consolidates duplicate scans at upload time. When a scan with identical results is uploaded:
- The system compares the scan summary plus 100 randomly-sampled controls from the existing scan
- If the data matches, the existing scan record is updated with an incremented
scanCountand updatedlastScannedAttimestamp - No new scan document is created, preventing database bloat from repeated identical scans
- The scan count badge shows how many times the same results were uploaded
Deduplication is particularly useful for scheduled scans that run daily or weekly. If your environment has not changed between scan cycles, the scan count increments without creating redundant records.
M365 Compliance Audit
The M365 cloud audit evaluates your Microsoft 365 tenant for compliance with CIS Benchmarks, CISA SCuBA baselines, and DISA STIGs across eight application areas.
Running the Audit Script
# Basic usage - interactive authentication
.\M365-ComplianceAudit.ps1 -TenantId "your-tenant-id" -OutputDir "C:\ScanResults"
# App-only authentication with certificate
.\M365-ComplianceAudit.ps1 -TenantId "your-tenant-id" -AppClientId "app-client-id" -CertThumbprint "thumbprint" -OutputDir "C:\ScanResults"
# Scope to specific applications
.\M365-ComplianceAudit.ps1 -TenantId "your-tenant-id" -Applications "EXO,SPO,DEF" -OutputDir "C:\ScanResults"Script Parameters
| Parameter | Type | Required | Description |
|---|---|---|---|
-TenantId | String | Yes | Azure AD tenant ID (GUID) |
-OutputDir | String | No | Directory for scan output (default: current directory) |
-AppClientId | String | No | App registration client ID for app-only auth |
-CertThumbprint | String | No | Certificate thumbprint for app-only auth |
-Applications | String | No | Comma-separated list of apps to scan (ENT, EXO, SPO, SPT, DEF, PUR, PBI, PPL) |
Applications Scanned
| Code | Application | Controls |
|---|---|---|
ENT | Entra ID (Azure AD) | Identity, MFA, conditional access, privileged roles |
EXO | Exchange Online | Mail flow, transport rules, auditing, DKIM/DMARC/SPF |
SPO | SharePoint Online | External sharing, guest access, DLP policies |
SPT | Teams | Meeting policies, messaging, external access, guest settings |
DEF | Defender | Safe Links, Safe Attachments, anti-phishing, preset policies |
PUR | Purview | DLP policies, retention, sensitivity labels, audit logging |
PBI | Power BI | Publish to web, resource key auth, external sharing |
PPL | Power Platform | Environment security, DLP policies, connector restrictions |
Approximately 36 Teams controls that use Cs* cmdlets (e.g., Get-CsTeamsMeetingPolicy) require delegated authentication and cannot run in Azure Automation. These controls will permanently return "Skip" status in automated scans.
Endpoint Vulnerability Scanning
The endpoint scan collects vulnerability, software inventory, and compliance data from Microsoft Defender for Endpoint (MDE) and Microsoft Intune.
Data Sources
- MDE Devices: Full device inventory with health status, risk score, and exposure level
- MDE Vulnerabilities: Per-device CVE data queried individually to avoid memory limits
- MDE Software: Installed software inventory with weakness counts
- CISA KEV: Known Exploited Vulnerabilities catalog cross-referenced with MDE CVEs
- Intune Devices: Managed device compliance status and configuration profiles
Schedule
The Scan-Endpoints runbook runs daily at 3:00 AM ET via the daily-endpoint-scan Azure Automation schedule. Results are automatically uploaded to the TATER API.
Speed Test
The TATER Agent includes a built-in network speed test that measures download bandwidth. Results are uploaded alongside compliance scan data.
- Uses self-hosted test files at
/Agent/speedtest/100mb.binand50mb.binhosted on the TATER marketing SWA - No dependency on third-party services (Cloudflare speed test caps at ~25MB)
- Results include download speed in Mbps and latency measurements
- Speed test scans appear in their own group on the Scans page
CSV Export
Export scan results to CSV format for use in external tools, SIEMs, or data warehouses:
- Navigate to a specific scan's detail view
- Click the Export CSV button in the toolbar
- The CSV includes all control evaluations with: Control ID, Title, Status, Severity, Framework, Application, Description, and Remediation guidance
You can also export from the Controls page to get a cross-scan view of all controls and their current status.
Scan Scheduling
Configure recurring scan schedules using the Azure Automation scheduling system:
| Schedule | Frequency | Time (ET) | Runbook |
|---|---|---|---|
weekly-m365-scan | Weekly (Sunday) | 2:00 AM | Scan-M365Cloud |
daily-endpoint-scan | Daily | 3:00 AM | Scan-Endpoints |
TATER also supports server-side scan scheduling through the GET/POST /scan-schedule API endpoints for organizations that prefer to manage schedules within the TATER application.
For detailed instructions on setting up Azure Automation runbooks for scheduled scanning, see the Azure Runbooks guide.
 TATER
TATER